Proxies are no longer just a convenient option—they’ve become essential tools for modern business operations. Choosing the right proxy ensures secure access to external resources, automates workflows, and collects critical data while minimizing risks and costs.
Proxies strengthen corporate security. They conceal real IP addresses of employees and servers, reduce exposure to attacks, mitigate DDoS and targeted intrusions, and provide centralized traffic management and filtering for incoming and outgoing connections.
For scaling operations, proxies enable load distribution across large volumes of automated requests and help overcome speed and request limits. Proper use ensures service stability under heavy workloads and reduces the likelihood of bans from external platforms.
From an analytics standpoint, proxies provide access from multiple locations and IPs, improving the accuracy of price monitoring, ad verification, and competitive intelligence. Without proxies, results can be skewed by caching or personalized content, whereas a well-configured proxy delivers reliable and comparable data.
Proxies in a Business Context
In business, a proxy acts as an intermediary between your systems (or employees) and external online resources. Requests routed through a proxy do not come from your real IP but from the proxy server’s address. Proxies can filter, cache, log traffic, manage geolocation, and handle sessions.
Personal vs. Corporate Proxy Use
For individual users, a simple proxy often suffices: one or two IPs for privacy or bypassing geo-restrictions, configured in a browser for occasional requests. Business needs are far more complex.
Companies require large IP pools, automatic rotation to prevent blocks during mass requests, high speed, reliability, logging for audits, and integration with internal systems. Business proxies also often play a role in security, concealing servers, filtering traffic, and controlling access.
Corporate proxies are typically integrated into automated processes (scripts, scrapers), offer API management, vendor support, and often comply with legal requirements and regulations.
- In short, personal users prioritize simplicity and privacy, while businesses need scalability, management, reliability, and regulatory compliance.
Business Use Cases for Proxies
Proxies address a wide range of business challenges, from protecting infrastructure to ensuring data accuracy and supporting automated workflows.
Security and Infrastructure Protection
Proxies provide the first line of defense, enabling centralized blocking of unsafe sites, filtering malicious traffic, logging connections for audits, and reducing the attack surface.
Scaling Automation and Avoiding Blocks
High-volume requests (scraping, mass registrations, automated testing) quickly exceed limits on a single IP. Proxies distribute load across multiple addresses, rotate IPs automatically, and maintain stability for scripts and services, allowing scalable processes without interruptions.
Data Collection and Accurate Monitoring Across Locations
For price monitoring, ad verification, content checks, or competitive intelligence, proxies provide access from target regions and prevent distortions caused by caching, personalization, or geo-restrictions.
Testing, QA, and Development
Proxies allow testing service behavior from different regions, verifying localization, simulating network conditions, and conducting tests without exposing internal addresses. For example, you can test payment flows or content delivery from a regional IP without traveling physically.
Anti-Fraud and Competitive Protection
Proxies conceal internal addresses during external interactions, reducing risks of targeted attacks, data manipulation, or competitor monitoring.
Key Factors in Choosing a Business Proxy
When selecting a proxy for business, focus on technical and commercial criteria that impact efficiency and reliability:
- Reliability and speed ensure stable requests and timely responses.
- IP location matters when tasks require access from specific regions.
- Scalability and pool size are critical for large-scale automation.
- Protocol and authentication support guarantee compatibility with your tools—ensure the provider supports HTTP/HTTPS and SOCKS5 with convenient authentication and management APIs.
- Cost-effectiveness should consider total ownership, not just price per IP. Cheaper options may require extra maintenance, frequent switching, or downtime. Evaluate SLAs, support, logs, and monitoring tools for overall efficiency.
Belurk meets these requirements. It offers preconfigured geolocations for target markets, automatic IP rotation, and clear statistics to quickly identify and resolve issues before they impact business metrics. Integration with scrapers or CRMs is easy and secure through their APIs.
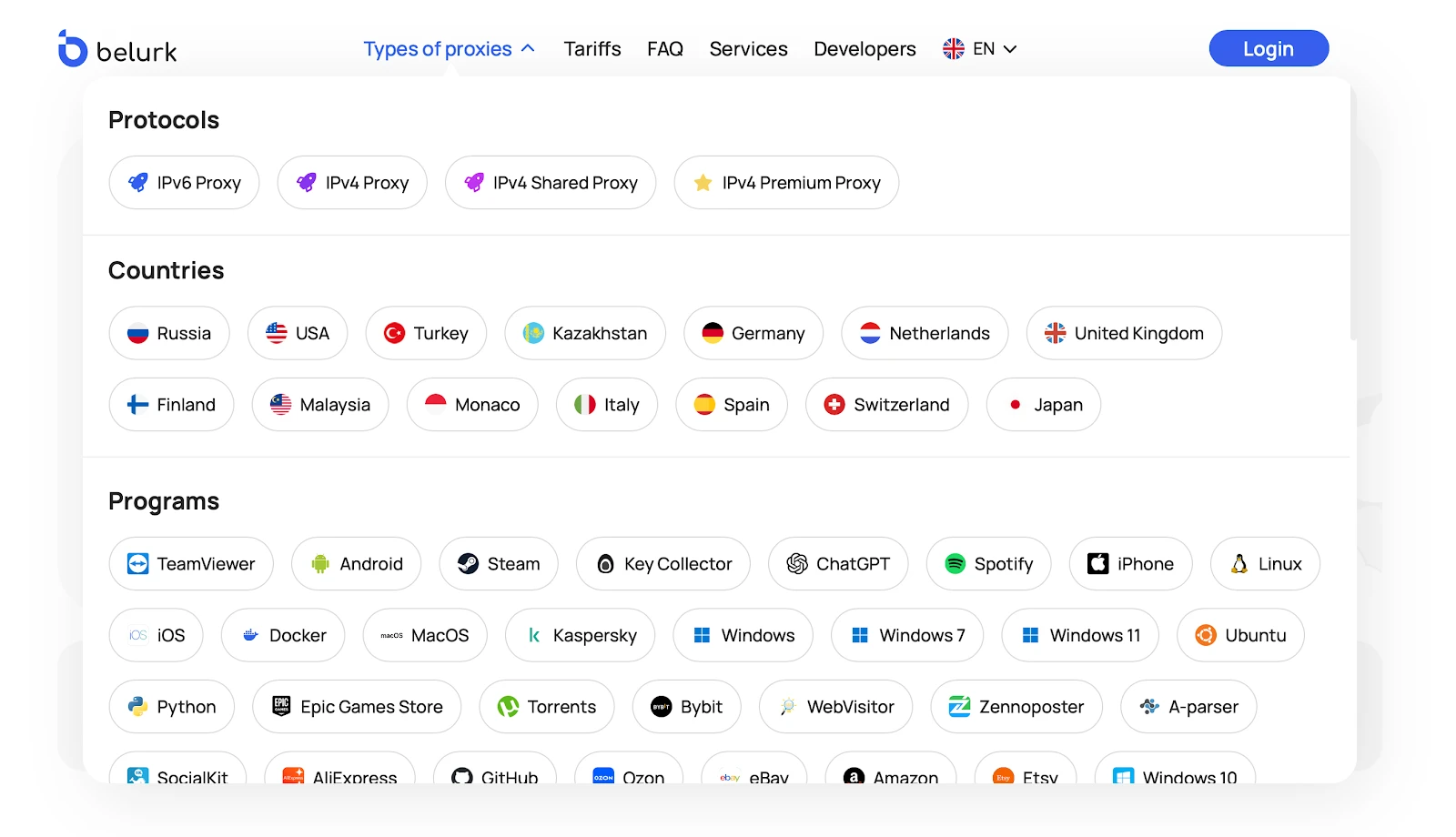
Geotargeting, multiple proxy types, management, and automation simplify the detection and reproduction of issues that real users encounter. Belurk is a practical and efficient solution for these tasks.
